Purpose:
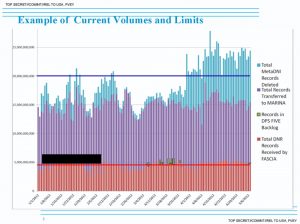
FASCIA is the US National Security Agency’s (NSA) data storage and analyse programme focused on mobile phone location metadata. Approximately 5 billion records per day are collected [WAH01]. The programme exploits the SS7 (Signaling System No. 7) data exchange protocol, which links mobile network providers together.
Two kinds of data are collected from mobile devices [WAH01].
- Information from phones, both mobile devices and landlines. This includes information held in these network such as location – known as Dialed Number Recognition (DNR) data.
- Information collected from the Internet – This includes personal data communications, known as Digital Network Intelligence (DNI).
Additionally it has the ability to analyse communication security (COMMSEC) behaviours such as Behaviours around communication security “frequent power-down, handset swapping, SMS behaviour” [NSA01].
The leaked documents show that the GCHQ works in partnership with the NSA in DNI collection, specifically to track location using the Google tracking cookie PREFID that is gathered with personal data communications. This cookie can be used to hack into devices [WAH02].
The FASCIA programme uses a variety of data analysis techniques to locate and track individuals using these two sources of data (DNR and DNI) including [WAH01; NSA01]:
- CHALKFUN: This is a ‘co-travel analytics’ tool that analyses “date, time, and network location of a mobile phone over a given time period, and then looks for other mobile phones that were seen in the same network locations around a one hour time window” [NSA01].
- DSD Co-Travel Analytic: Examines mobile Call Detail Records (CDRs) to predict “target locations and co-travelers by calculating time-based travel trajectories. Probable travel routes are calculated using observed locations and determining the most likely paths and travel times similar to that used in turn-by-turn navigation systems” [NSA01]. “The analytic predicts the approximate time that the target would theoretically arrive at each segment waypoint based on projected travel times between known locations.” It also “discovers candidate co-travellers that intersect locations along the buffered travel path.” The NSA whitepaper states that the “system has shown that more candidate co-travellers were discovered by analyzing the travel paths than by considering common meeting locations alone”. Future plans for the system include identifying “targets based on COMSEC behaviors such as identifying mobiles that are turned off right before convergence between two travel paths occurs”.
- TMI Co-Traveler Analytic: “The analytic is oriented to work on 7 to 30 days worth of regional collection.” It computes “target “closeness” based on latitude and longitude information.
- PACT NGA-NSA GATC Analytic: To identify Thuraya satellite phones.
- RT-RG Sidekicks: “compares average travel velocity between pairs of selectors to infer whether or not could co-travel would practically be possible. Locations are defined by CELL IDs (for GSM) or GEO-Hashes.”
- Scalable Analytics Tradecraft Center (SATC) Geospatial Lifelines Co-Travel QFD: This “applies the concept of “dwell times” to identify DNR co-travelers. Dwell times describe the time period spent at the beginning or ending destination. A location is considered a beginning or ending location if the dwell time at that location is greater than 2 hours.”
- SSG Common IMSIs Analytic: “Finds SIM card activity seen on cell tower panels in multiple areas (e.g.- border crossings commonly used by traffickers) … The analyst inputs areas of interest and time range. The analytic returns an excel file with a list of IMSIs seen in those areas at that time.”
- The Café project: “This analytic uses IP geolocation of active user/presence events as travel indication.” It focuses on targets who have travelled between two countries in a range of time between 30 days. It is also searchable by travel within “countries of interest” and “the days on which the countries were visited”.
- Other Data Sources: this includes information from other databases such as “air travelers on the same reservation number”, “users sharing a MAC address” and “similarities between IP addresses may indicate proximity on the same LAN” [NSA01].
Capabilities:
- Mobile phone network and internet analysis
- Pattern-of-life analysis
Data sources:
- Mobile networks
- GCID: Global Cell-Tower ID – This is the unique number associated with any given tower. It acts as a proxy for location since
- CELLID – mobile base station coordinates
- VLR – (Visitor Location Registers); databases that track current associations between cellular users and towers, which can be used to infer a user’s location
- IMSI – (International Mobile Subscriber Identity)
- MSISDN – the telephone number associated with a SIM card indicating the country it was activated in and the service provider
- Internet data transfer
- Mobile phone apps
- IP address
Related programmes:
R6 SORTINGLEAD – Cloud-based version of CHALKFUN that includes additional features such as search by countries or locations of interest [NSA01].
HAPPY FOOT – Analytic tool that aggregates leaked location-based service data to map the physical locations of IP addresses [WAH01].
TAPERLAY – The NSA’s tool for looking up the registered location of a mobile device — the provider and country where a phone was originally activated — in the Global Numbering Database [WAH01].
TUSKATTIRE – System used for metadata processing [WAH01]
JUGGERNAUT – A signals processing system that can process raw feeds between mobile carriers through the SS7 protocol [WAH01].
GHOSTMACHINE – The NSA’s cloud analytics platform [WAH03].
Layers of operation:
- Social layer: Aggregation of metadata from multiple sources, pattern-of-life analysis.
- Link layer – How devices connected to a physical layer share access to the physical medium and exchange data.
- Network layer – How data is routed between devices that may be connected to different link layers.
- Application layer – How applications provide services and exchange information over a transport layer.
Background:
FASCIA is the National Security Agency’s enormous database containing trillions of device-location records that are collected from a variety of sources. The leaked documents show the volume and types of device-location data collected. Mobile phone metadata analysis can reveal a high-level of detail regarding people’s movements.
When mobile devices are turned on and begin searching for wireless signals, they show their locations to any radio receivers in the vicinity. When a mobile phone connects to a network, it registers its location to one or more signalling towers that store this information in databases (known as Home Location Registers and Visitor Location Registers) maintained by telephone providers and clearing houses so that calls can be made and received.
These registers store a device’s approximate location using service providers positioning of devices by triangulating their distance between multiple towers in the vicinity. These can reveal the country, town, and even street level of the person. In addition, some mobile devices use WiFi and GPS signals to fix their locations, which provides geo-location data. Smartphones can also display their location through mobile apps, built-in location based services and IP addresses [WAH01].
Sources:
National Security Agency (NSA) document, (provided by the Washington Post)
1) National Security Agency white paper: Summary of DNR and DNI Co-Travel Analytics
https://s3.amazonaws.com/s3.documentcloud.org/documents/888734/cotraveler-tracking-redacted.pdf
Washington Post (WAH)
2) http://apps.washingtonpost.com/g/page/world/nsa-signal-surveillance-success-stories/647